The ultimate guide to cybersecurity defense

Cybersecurity threats have become increasingly varied and complex, making robust defense increasingly important. A strong cybersecurity posture helps businesses identify and respond to digital threats, minimizing the risk of financial loss, operational disruption, and reputational damage.
This guide explains what cybersecurity defense means, the common threats organizations face (along with effective defenses), how layered protection works, key technologies and frameworks, and how to build a comprehensive cybersecurity strategy.
What is cybersecurity defense?
Cybersecurity defense covers the processes and tools used to protect systems, devices, networks, data, and applications from all forms of cyber threats.
A cyber defense strategy harnesses a mix of people, processes, and technologies to manage and reduce risks, with a strong emphasis on identifying, preventing, detecting, responding to, and recovering from threats.
What are organizations defending against?
Organizations today face a broad spectrum of threats that target endpoints, networks, users, and data. These threats can originate from outside or inside the environment and follow diverse patterns, which is why a layered approach to defense is crucial.
The following sections describe some of the most common threats and include effective ways to guard against them.
Business email compromise (BEC), phishing, and social engineering
A BEC attack is a form of email-based fraud where attackers impersonate trusted figures, such as executives, vendors, or partners, to trick employees into taking a specific action, such as transferring money to an account or sharing sensitive information.
Social engineering is the broader category that includes these tactics, as well as building trust via email, calls, or other channels to manipulate victims into revealing sensitive data such as credentials.
Defense mapping
- Phishing-resistant multi-factor authentication (MFA) to reduce the risk of unauthorized access and prevent account takeovers.
- Email filtering systems to detect and block suspicious messages.
- Regular employee security awareness training.
- Security information and event management (SIEM) systems to monitor and correlate events, including unusual login patterns.
- Zero-trust identity verification to validate all access requests.
- Clear incident-reporting workflows for a quick response when credentials are compromised.
Supply chain attacks
These target key entities throughout the supply chain (partners, suppliers, or vendors), often by compromising software, updates, or trusted third-party access, which can provide attackers with trusted access to internal systems and enable further compromise.
Defense mapping
- Network segmentation to isolate and limit the spread of compromise.
- Endpoint detection and response (EDR) solutions to monitor devices for abnormal behavior.
- Zero-trust architecture to reduce implicit trust in vendor access by continuously validating requests and interactions.
- Supplier risk management practices, such as vendor assessments and software integrity verification.
Insider threats
These come from employees, contractors, or other trusted users who, intentionally or accidentally, use their trusted access to steal data, spread malware, or cause other harm; such threats are harder to spot because of the insider's legitimate privileges.
Learn more: Insider threats – prevention and management
Defense mapping
- Role-based access controls (RBAC) to restrict data and application access as needed.
- User behavior analytics systems to detect and alert on abnormal internal activity.
- Data loss prevention (DLP) tools to block unauthorized data transfers.
- Logging and monitoring solutions (including SIEM) to track and flag suspicious actions.
- Access reviews and offboarding procedures to remove or adjust permissions when roles change or employment ends.
Tailgating
Tailgating is a physical security breach. An unauthorized person follows an authorized individual into a restricted area, such as an office or server room, to gain physical access to systems, devices, data, or network infrastructure.
Defense mapping
- Physical measures, like secure badge access controls for individual authentication at entry points.
- Security awareness training to remind employees not to share access privileges or allow unauthorized entry.
- Surveillance systems, such as cameras to monitor secure areas and detect unauthorized attempts.
- Visitor management procedures, such as sign-in logs and escorted access for guests.
How layered defense works
Modern organizations avoid relying on a single solution and instead deploy multiple interconnected, overlapping protections across data, devices, networks, applications, identities, and users.
In this layered approach, even if an attacker breaches one barrier, additional layers remain to help limit further progress and damage.
For example, a phishing attack might yield an employee's credentials, but MFA and network monitoring can still reduce the risk of account takeover or large-scale data exfiltration.
What are the layers of cybersecurity defense?
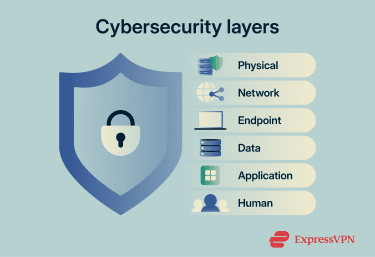
- Physical: Real-world protections such as keycards, locked doors, access badges, and cameras.
- Network: Tools used for monitoring and securing traffic, including intrusion detection systems, firewalls, and network segmentation.
- Endpoint: Device-level security, like antivirus software and endpoint monitoring applications.
- Data: Safeguards such as encryption, access controls, and DLP systems.
- Application: Protections such as application firewalls and cloud protection measures.
- Human: Training and courses to build employee awareness of cybersecurity practices, policies, and risk management.
Importance in today’s digital landscape
Businesses depend heavily on interconnected systems and devices for daily operations, and any compromise through cyberattacks, ransomware, or data leaks may lead to financial and reputational harm. Customers and users could also be exposed to risks such as identity theft or fraud if protections fail.
Overall, organizations now face stricter regulations and compliance requirements, making cybersecurity a top priority.
Emerging technologies like AI are also enabling more sophisticated attacks (such as AI phishing), while advances in quantum computing promise even greater challenges ahead. As such, both organizations and individual users need to stay vigilant and proactive against these evolving risks.
Technologies used in cybersecurity defense
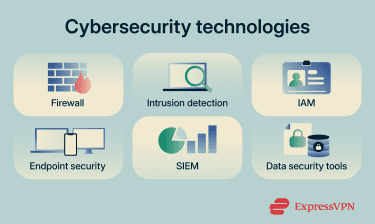 Cybersecurity tools range from passive monitoring solutions that analyze activity for suspicious signs to proactive ones that block unauthorized access. Key categories include the following:
Cybersecurity tools range from passive monitoring solutions that analyze activity for suspicious signs to proactive ones that block unauthorized access. Key categories include the following:
- Firewalls and intrusion detection systems: Monitor and control network traffic, filter out malicious or unauthorized traffic based on security rules, detect attack patterns, and either alert teams or actively block threats.
- Endpoint security solutions: Protect individual devices such as laptops, smartphones, and servers. Includes endpoint protection platforms (EPP), endpoint detection and response (EDR), extended detection and response (XDR), and antivirus programs.
- SIEM systems: Centralize security monitoring by collecting and analyzing logs from endpoints, networks, applications, and other sources to identify anomalies, correlate events, generate real-time alerts, and provide comprehensive visibility into the organization's security posture.
- Security Orchestration, Automation, and Response (SOAR) systems: Build on SIEM data and other inputs by automating investigations, orchestrating workflows across tools, executing predefined playbooks, and speeding up incident response to reduce manual effort and support more efficient incident response.
- Identity and access management (IAM): Controls such as authentication, MFA, single sign-on (SSO), and privileged access management (PAM) to manage user identities and access.
- Data security tools: Technologies such as encryption and DLP to protect sensitive data at rest, in transit, and in use.
How frameworks formalize cybersecurity defense
With so many threats and tools available, organizations benefit from structured guidance on implementation and improvements. Cybersecurity frameworks serve as comprehensive, structured guidance that outlines best practices, supports audits of current defenses, and facilitates adaptation to new risks.
Comprehensive frameworks address governance, risk management, threat detection, prevention, and response, while others prioritize specific controls or adopt an attacker's perspective by mapping common attack stages.
The common frameworks detailed below are often used together. For example, the National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) for overall strategy, CIS Controls for prioritized implementation, and MITRE ATT&CK or Cyber Kill Chain for threat-informed detection and response.
NIST CSF 2.0
CSF 2.0 offers flexible guidelines for organizations of all sizes and industries to manage cybersecurity risk across threats like phishing, malware, and insider risks through six core functions:
- Govern: Establishes cybersecurity risk management strategy, policy, roles, and oversight at the executive level.
- Identify: Develops understanding of assets, risks, and business context to prioritize efforts.
- Protect: Implements safeguards such as access controls, training, and data security to limit the impact.
- Detect: Enables timely discovery of events through monitoring and anomaly identification.
- Respond: Contains and mitigates incidents through structured processes and communications.
- Recover: Restores capabilities and improves resilience after an event.
Learn more: Understanding NIST CSF – a full guide
Center for Internet Security (CIS) Controls
CIS Controls provide 18 actionable measures developed by global experts to defend against prevalent cyberattacks, covering areas like data protection, account management, vulnerability management, malware defenses, and incident response.
It's particularly practical for quick prioritization and mapping to other frameworks, such as the NIST CSF.
Cyber Kill Chain
The Cyber Kill Chain from Lockheed Martin describes seven sequential steps attackers often follow:
- Reconnaissance
- Weaponization
- Delivery
- Exploitation
- Installation
- Command and control
- Actions on objectives
With this framework, teams can visualize campaigns and disrupt and delay attacks at multiple points in this cycle. It's linear and useful for understanding attack progression, though modern threats may not always follow strict sequences.
Learn more: Cyber Kill Chain: How attacks work and how to stop them
MITRE ATT&CKⓇ
MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) is an evolving framework that details attacker tactics, including reconnaissance, privilege escalation, lateral movement, and exfiltration.
More detailed than the Cyber Kill Chain, this framework enables teams to model threats, detect behaviors, and test defenses against known techniques. It's widely used for threat hunting, detection engineering, and mapping real-world adversary behaviors.
How to develop a cybersecurity defense strategy
 A strong strategy integrates frameworks, technologies, and best practices into a unified, risk-focused program that addresses the organization's specific risks and supports overall goals. The process typically includes these key steps:
A strong strategy integrates frameworks, technologies, and best practices into a unified, risk-focused program that addresses the organization's specific risks and supports overall goals. The process typically includes these key steps:
- Assess current security posture: Evaluate strengths, identify weaknesses, and plan ways to address them.
- Outline clear objectives: Set goals based on business size, industry, and priorities, such as protecting sensitive data, achieving regulatory compliance, or reducing incident frequency.
- Develop a risk management plan: Identify threats, assess their likelihood and potential impact, and prioritize the highest risks.
- Implement appropriate tools and controls: Deploy SIEM for monitoring, endpoint protection, zero-trust architecture, and other solutions based on the identified risks.
- Educate employees: Conduct regular security training and awareness sessions to build knowledge of threats, safe habits, and reporting procedures.
- Prepare for and respond to incidents: Monitor systems for early detection and follow predefined incident response workflows. This includes processes to help contain incidents, limit spread, support recovery, and incorporate lessons learned.
- Iterate and improve: Track systems over time, conduct ongoing monitoring, address emerging weaknesses, and adapt defenses to new attack methods and technologies.
Best practices for cybersecurity defense
Maintaining strong defenses requires ongoing commitment amid evolving threats. Organizations should conduct regular security audits, including penetration tests and vulnerability scans, to uncover and fix weaknesses.
Employee training and awareness programs remain essential, as the human element continues to account for a large portion of breaches, according to the Verizon 2025 Data Breach Investigations Report, often due to errors, social engineering, or misuse.
Proactive risk management helps evaluate threats by likelihood and impact to guide resource allocation effectively.
Additional measures include enforcing strict access controls, applying regular software and hardware updates, and leveraging layered tools such as firewalls and SIEM systems.
FAQ: Common questions about cybersecurity defense
What is a cybersecurity defender?
What is a cybersecurity defender?
What are the key technologies used in cybersecurity defense?
What are the common cyber threats to organizations?
What are some best practices for maintaining cybersecurity?
How is AI changing cybersecurity?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN